MTK Auth Bypass Tool V170 Is A Robust Software Developed Specifically For Mediatek And Unisoc Devices, Featuring Nv Manager, Meta Mode, And Partition Manager. No. Whether You Are Working With Huawei, Xiaomi, Samsung, Or Qualcomm Products, This Tool Provides Essential Firmware Utilities And Flashing Capabilities That Ensure Seamless Device Access.
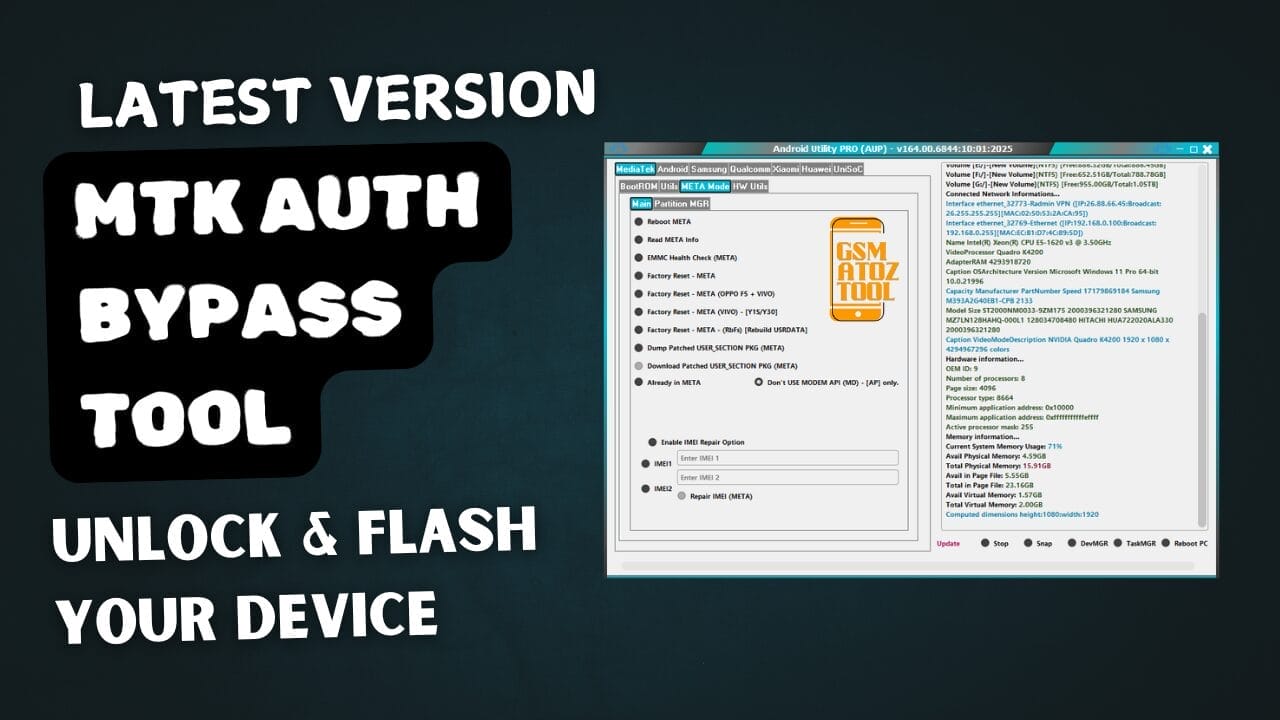
Mtk auth bypass tool latest version unlock your device
Contents
- 1 Download MTK Auth Bypass Tool Latest Version
- 1.1 What Is The MTK Auth Bypass Tool
- 1.2 Features of Android Utility Pro Tool
- 1.2.1 MediaTek[BootRom]
- 1.2.2 NV Manager
- 1.2.3 META Mode [Main]
- 1.2.4 Partition MGR
- 1.2.5 Huawei
- 1.2.6 Android [Main]
- 1.2.7 MTP AOA
- 1.2.8 Tools
- 1.2.9 Firmware Utils
- 1.2.10 Samsung [Main]
- 1.2.11 MediaTek
- 1.2.12 UniSoC
- 1.2.13 Flasher
- 1.2.14 Qualcomn
- 1.2.15 Xiaomi
- 1.2.16 NV MANAGER
- 1.2.17 Xiaomi [Main]
- 1.2.18 Flasher
- 1.2.19 Service
- 1.2.20 Firmware Reader
- 1.2.21 UniSoc
- 1.3 How To Use
- 1.4 How To Download
Download MTK Auth Bypass Tool Latest Version
Downloading The Latest Version Of The Mtk Auth Bypass Tool Offers Users An Array Of For Mediatek Devices. These Powerful Features Include Bootrom Access And Nvm Manager, Which Ensure Smooth Interactions With Device Firmware; Meta Mode Serves As Its Main User Interface, Enabling Efficient Manipulation Of Components.
Partition Mgr Allows For Efficient Device Partition Management And Is Compatible With Many Brands, Including Huawei, Xiaomi, And Samsung. Users Can Utilize Mtp Aoa Features And Various Tools Such As Flasher Options And Firmware Utils To Enhance Functionality Further.
The Tool Supports Qualcomm And Unisoc Devices, Providing Users With A Wider Application. Of Its Many Features, Firmware Reader And Service Are Especially Helpful For Advanced Users Seeking To Alter Or Recover Device Firmware.
Also Read
What Is The MTK Auth Bypass Tool
The Mtk Auth Bypass Tool Is An Efficient Way Of Bypassing Authentication Protocols On Mediatek Devices, Providing Easier Access To Firmware Updates And System Functions. Utilizing Bootrom Exploits To Manipulate Meta Mode; Users Gain The Power To Manage Partitions Via Partition Mgr While Taking Advantage Of Nv Manager Features For Device Configuration.
This Tool Is Especially Beneficial To Huawei, Xiaomi, And Samsung Users As It Offers Essential Firmware Utilities And Service Options. Qualcomm And Unisoc Platforms Are Supported, Providing A Versatile Solution For Various Android Devices. Mtp Aoa And Firmware Reader Functions Help Streamline Flashing Or Modifying Device Firmware Updates.
Features of Android Utility Pro Tool
MediaTek[BootRom]
- Disable Auth
- Dump Preloader (EMI) For Test -Point
- Crash Preloader To BRom
- Reboot AT Mode
- Reboot Factory Mode
- Reboot Fastboot Mode
- Read Device Info (BootROM)
- (eMMC/UFS) Health Check (BootROM)
- Read (eMMC/UFS) [USER_SECTION] Dump (USB) [16MB]
- Write (eMMC/UFS) [USER_SECTION] Dump (USB)
- Read (eMMC/UFS) [USER_SECTION] (LUNO/BOOT1)
- Write (eMMC/UFS) [USER_SECTION] (LUNO/BOOT1)
- Disable Orange State [BootROM]
- Restore Orange State [BootROM]
- Disable Dm _Verity [BootROM]
- Fix (OPPO/Realme)
- VIVO New SEC Readinfo (FM)
- VIVO (MT6771/MT6765) Force BRom
- VIVO (MT6771/MT6765) Exit BRom
- VIVO (MT6771/MT6765) Remove Demo
- OPPO MT6771 Force BRom (PL) [F7,F9]
NV Manager
- Backup NVRAM_NVDATA [BROM]
- Restore NVRAM_NVDATA [BROM]
- Restore NVRAM_NVDATA [Fastboot]
- Format NVMM_NVDATA [BROM]
- Format NVRAM_NVDATA [Fastboot]
- Fix (unknown baseband) [BROM]
- Fix (unknown baseband) [Fastboot]
META Mode [Main]
- Reboot META
- Read META Info
- EMMC Health Check (META)
- Factory Reset – META
- Factory Reset – META (OPPO F5 + VIVO)
- Factory Reset – META (VIVO) – [Y1S/Y30]
- Factory Reset – META – (RbFs) [Rebuild USERDATA]
- Dump Patched USER_SECTION PKG (META)
- Download Patched USER_SECTION PKG (META)
- Enable ADB Debug (META)
- Already in META
- Don’t USE MODEM API (MD) – [AP] only.
Partition MGR
- Format PART (META)
- Read PART (META)
- Write PART (META)
- Dump USERAREA (META)
- Dump PGPT (META)
- Dump NV Regions (META)
- Dump EXT_CSD (META)
- Dump MDDB/APDB (META)
- Read NVRAM (META)
- Write NVRAM (META)
- Wipe NVRAM (META)

Mtk auth bypass tool
Huawei
- Huawei Y9A (FRL-L22) Force BRom
- Huawei Y9A (FRL-L22) Exit BRom
- Honor X6 (VNE-LX2) Force BRom
- Honor X6 (VNE-LX2) Exit BRom
Android [Main]
- ADB Read Info
- ADB Reboot to
- ADB Reboot to Recovery
- ADB Reboot to EDL
- ADB G-Lock Bypass
- ADB Factory Reset (Old Android)
- Fastboot Read Info
- Fastboot Flash Partition
- Fastboot Set Active Slot [A]
- Fastboot Set Active Slot [B]
- Fastboot Fix DM-Verity Error
- Exit Fastboot Mode
- Xiaomi Enable Diag (ADB)
- Install APK (Adb)
- Generic Fastboot Factory Reset
- Generic Fastboot G-Lock Wipe
- Disable Payjoy APP (ADB)
- Vivo Demo Remove (MT6877T)
- Vivo Demo Remove (AT)
- RealME (Wireless Test Assistant mode) Disable
MTP AOA
- MTP Launch Browser (GENERIC) [YouTube]
- MTP Launch Browser (GENERIC) [Google Maps]
- MTP Launch Browser (GENERIC) [GooglePlay]
- Enter URL
- Enter VID
- Enter PID
- MTP Launch Browser (custom URL)
- MTP Launch Browser (By VID _PID)
Tools
- Decode Android (gesture.key) [Android 6]
- Decode Android (contacts.db) to [VCF Card)
Firmware Utils
- Extract Samsung ROM (MTK)
- Extract Huawei UPDATE (MTK)
- Extract [OPPO/Realme] ROM (MTK + QCOM) (.ofp,.ozip)
- Extract LG ROM (.kdz)
- Extract OnePlus ROM (.ops)
- Extract RedMagic (payload.bin)
- Extract (Spreadtrum/UniSoC) (.pac)
- Extract MTK Preloader from (BOOT1&LUN0)
- Extract Super IMG
- Extract (eMMC/UFS) Dump
- MTK PGPT to Scatter (eMMC)
- MTK Scatter to PGPT (eMMC)
- MTK Create BOOT SECTION from Preloader
- Parse MTK Preloader
- Parse MTK DA
Samsung [Main]
- Samsung Read Info (MTP)
- Samsung Read Info (DM)
- Samsung Reboot MTP to (DM)
- Samsung F-Reset (MT P)
- Samsung Enable ADB (MTP)
- Samsung Enable ADB New SEC (MTP)
- Samsung Enable ADB New SEC [JUNE 2023 (MTP)
- Samsung Change SN {ADB}
- Samsung Read EFS {ADB}
- Samsung Restore EFS {ADB}
- Samsung Restore NV-DATA {ADB}
MediaTek
- Samsung MTK Force BRom – BL (DM)
- Samsung MTK Force BRom – PGPT (DM)
- Samsung MTK PRELOADER Repair via BL (FM)
- Samsung MTK GPT Repair via CSC (FM) [eMMC only)
- Samsung [SM-GS32F] Force BRom (FM)
- Samsung [SM-G532F] Boot Repair
- Samsung [SM-A226B-B5] Boot Repair
- Samsung [SWA326U-B7] Boot Repair
- Samsung [SWA326U-B8] Boot Repair
- Samsung MTK Rebulid PMT (DM)
- Samsung MTK Exit BRom (FM)
- Samsung [SM-A037F-B2] (SEC CTRL 0) Unlock Bootloader (FM)
- Samsung [SM-A037F-B2] (SEC CTRL 0) Block Hosts (FM)
- Samsung [SM-A037F-B2] Boot Repair
- Samsung[SM-A037U-B3] Boot Repair
- Samsung [SM-A037F] (SEC CTRL 0) Clear RPMB (PRELOADER)
- Samsung [SM-A042F] (SEC CTRL 0) Clear RPMB (PRELOADER)
- Samsung [SM-A226B] (SEC CTRL 0) Clear RPMB (PRELOADER)
- Samsung [SM-A037F] (SEC CTRL 0) WRITE RPMB (PRELOADED)
- Samsung [SM-A042F] (SEC CTRL 0) WRITE RPMB (PRELOADED)
- Samsung (SM-A226B] (SEC CTRL 0) WRITE RPMB (PRELOADED)
UniSoC
- Samsung UniSoC A03 (A035F) Boot Repair (FM)
- Samsung UniSoC A03 Core (A032F) Boot Repair (FM)
- Samsung UniSc Boot Repair via BL (FM)
- Samsung UniSoC Clear RPMB via BL (FM)
- Samsung UniSoc Unlock Bootloader (FB)
- Samsung UniSoc Relock Bootloader (FB)
- Samsung UniSoC Write PAC file
- Samsung UniSoC (X200f/205) Force BRom (DM)
- Samsung UniSoC (X200/X205) Exit BRom (FW/FDL)
- Skip EMMC PMT rebuild (UniSoC) [M] Versions.
Flasher
- Firmware Update (DM)
- Reboot Mode
- Repartition
- Boot Update
- Erase All
- Multi DL
- Clear EFS
- Reboot
Mtk auth bypass tool latest version
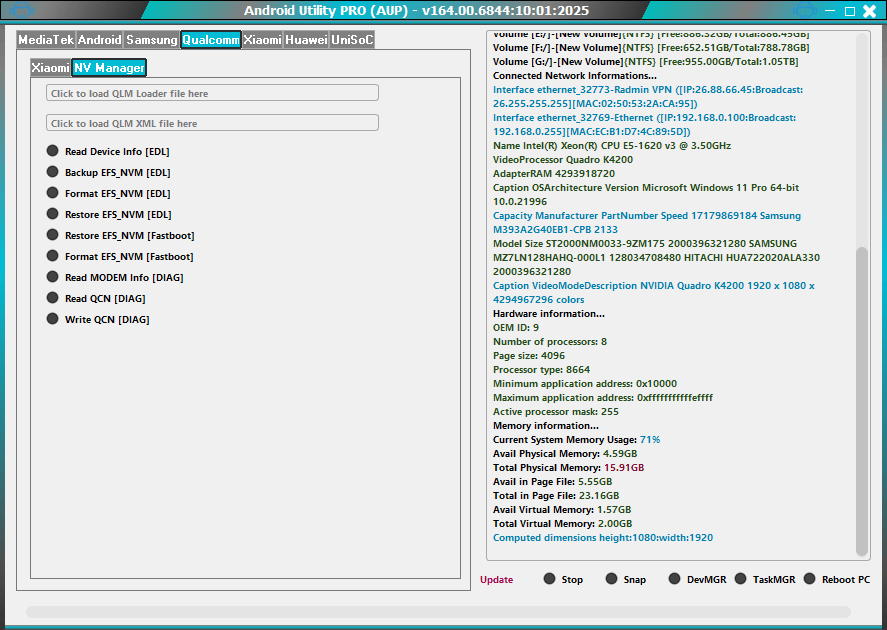
Qualcomn
Xiaomi
- Patch Xiaomi Qualcomm MI Account Lock
NV MANAGER
- Click to load QLM Loader file here
- Click to load QLM XML file here
Xiaomi [Main]
- Disable Xiaomi OTA updates [BootROM]
- Enable Xiaomi OTA updates [BootROM]
- Xiaomi 11T (agate) Re-Lock Bootloader
- Xiaomi 11T (agate) Unlock Bootloader
- Redmi Note 11 Pro 5G (pissarro) Re-Lock Bootloader
- Redmi Note 11 Pro 5G (pissarro) Unlock Bootloader
- Redmi Note [11/11T] 5G (evergo) Unlock Bootloader
- Redmi Note [11/11T) 5G (evergo) Re—Lock Bootloader
- Redmi Note [12] PRO 5G (ruby) Unlock Bootloader
- Redmi Note [121 PRO 5G (ruby) Re—Lock Bootloader
- Redmi 6A (cactus) Unlock Bootloader
- Xiaomi Check Find Status {Fastboot}
Flasher
- Firmware Update (Fastboot)
- Auto RebootHuawei [Flasher]
- Load Firmware Package
- Firmware Update (DLOAD)
- Flash Board Software (FB)
- Switch From FB
- Firmware Update (FB)
- Skip (OEM/NV)
- Extract Update
- Auto Reboot
Service
- Huawei Normal To Upgrade
- Huawei Fastboot To Upgrade
- HiSi1icon (USB 1.0)
- Load Factory Fastboot
Firmware Reader
- Read GPT
- Read
- Write
- Erase
- Reboot Device
UniSoc
- (Spreadtrurn/UniSoC) Write PAC file [FM]
- (Spreadtrum/UniSoC) Read Info [DIAG]
- (Spreadtrum/UniSoC) Wipe Data [DIAG]
How To Use
- You Will Need To First Download The Zip From The Below Link.
- Then, Unzip All The Files In The C Drive.
- Then, Install The Setup With The Basic Instructions.
- Run The Tool As Admin “MTK Auth Bypass Tool.exe“
- If You Already Have Drivers Installed, Skip This Step.
- Enjoy ! !!
How To Download
To Download MTK Auth Bypass Tool Follow These Steps:
- Go To The Gsmatoztool.com Website Of MTK Auth Bypass Tool.
- Find The Download Page And Don’t Click Button And Click Only The (Download Link)

- Wait For The Download To Complete.
- Locate The Downloaded File On Your Device Once The Download Is Finished.
- Double-click On The File To Start The Installation Process.
- Follow The On-screen Instructions To Complete The Installation.
MTK Auth Bypass Tool V170
Download Link:: Usersdrive – Mediafire – FastuUpLoad – Sendcm – TeraBox – 4Shared – Mega – PlayBook








